"The road to exploitable bugs is paved with unexploitable bugs."
-- Mark Dowd
Rhabdomancer is a blazing fast IDA Pro headless plugin that locates calls to potentially insecure API functions in a binary file. Auditors can backtrace from these candidate points to find pathways allowing access from untrusted input.
- Blazing fast, headless user experience courtesy of IDA Pro 9 and Binarly's idalib Rust bindings.
- Support for C/C++ binary targets compiled for any architecture implemented by IDA Pro.
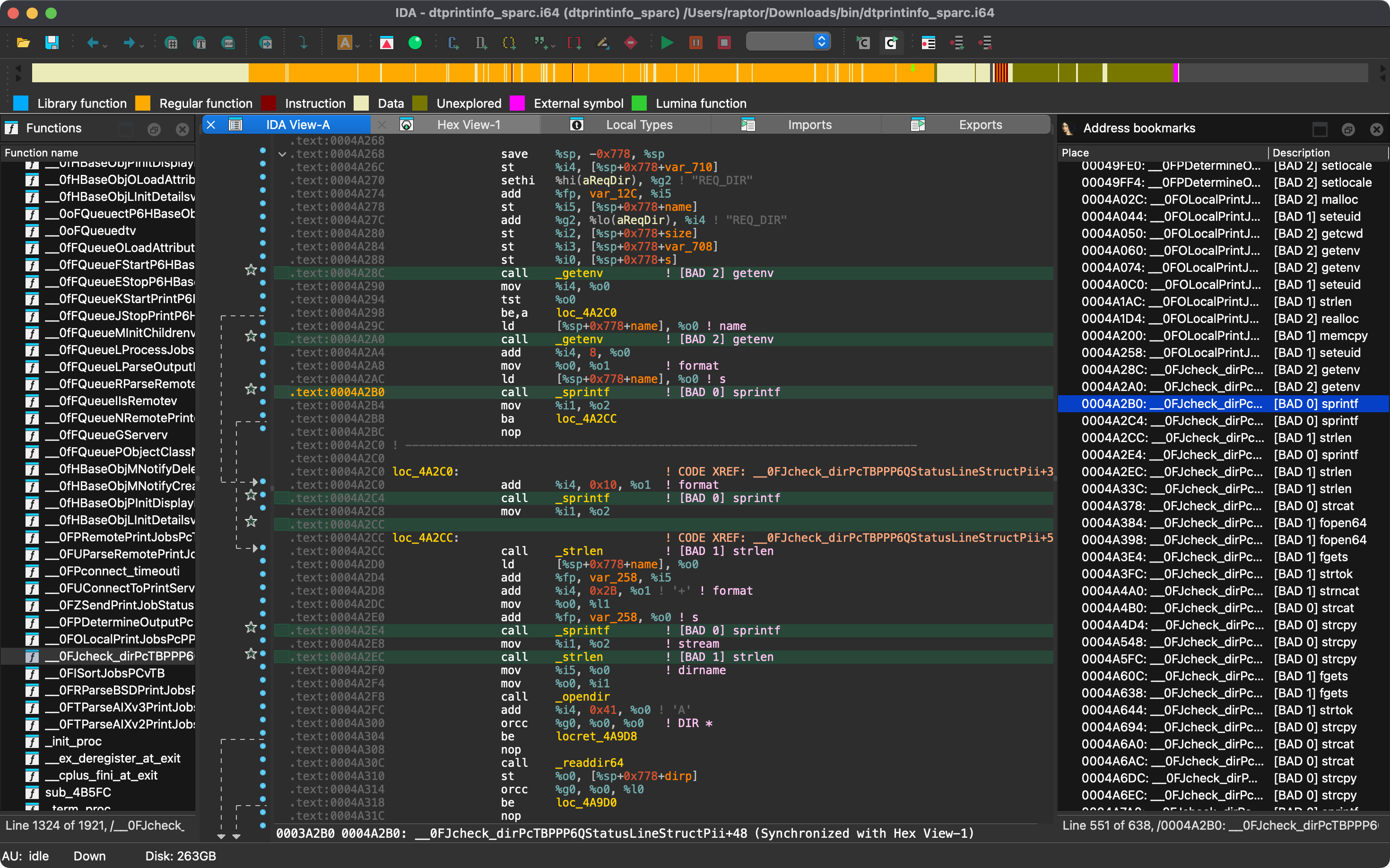
- Bad API function call locations are printed to stdout and marked in the IDB.
- Known bad API functions are grouped in tiers of badness to help prioritize the audit work.
- [BAD 0] High priority - Functions that are generally considered insecure
- [BAD 1] Medium priority - Interesting functions that should be checked for insecure use cases.
- [BAD 2] Low priority - Code paths involving these functions should be carefully checked.
- The list of known bad API functions can be easily customized by editing
conf/rhabdomancer.toml.
- https://github.com/0xdea/ghidra-scripts/blob/main/Rhabdomancer.java
- https://docs.hex-rays.com/release-notes/9_0#headless-processing-with-idalib
- https://github.com/binarly-io/idalib
- https://books.google.it/books/about/The_Art_of_Software_Security_Assessment.html
The easiest way to get the latest release is via crates.io:
- Download, install, and configure IDA Pro (see https://hex-rays.com/ida-pro).
- Download and extract the IDA SDK (see https://docs.hex-rays.com/developer-guide).
- Install rhabdomancer as follows:
$ export IDASDKDIR=/path/to/idasdk90 $ export IDADIR=/path/to/ida # if not set, the build script will check common locations $ cargo install rhabdomancer
Alternatively, you can build from source:
- Download, install, and configure IDA Pro (see https://hex-rays.com/ida-pro).
- Download and extract the IDA SDK (see https://docs.hex-rays.com/developer-guide).
- Compile rhabdomancer as follows:
$ git clone https://github.com/0xdea/rhabdomancer $ cd rhabdomancer $ export IDASDKDIR=/path/to/idasdk90 # or edit .cargo/config.toml $ export IDADIR=/path/to/ida # if not set, the build script will check common locations $ cargo build --release
- Make sure IDA Pro is properly configured with a valid license.
- Customize the list of known bad API functions in
conf/rhabdomancer.tomlif needed. - Run rhabdomancer as follows:
Any existing
$ rhabdomancer <binary_file>
.i64IDB file will be updated; otherwise, a new IDB file will be created. - Open the resulting
.i64IDB file with IDA Pro. - Select
View>Open subviews>Bookmarks - Enjoy your results conveniently collected in an IDA Pro window.
Note: rhabdomancer also adds comments at marked call locations.
- IDA Pro 9.0.240925 on macOS arm64 and Linux x64.
- IDA Pro 9.0.241217 on macOS arm64 and Linux x64.
Note: only the unix target family is currently supported, check idalib
documentation if you want to port it to windows yourself.
- Implement support for the
windowstarget family. - Enrich the known bad API function list (see https://github.com/0xdea/semgrep-rules).
- Implement a basic ruleset in the style of VulFi and VulnFanatic.